Website Information
1 |
http://result*****.SPR.GOV.MY |
The software constructs all or part of an SQL command using externally-influenced input from an upstream component, but it does not neutralize or incorrectly neutralizes special elements that could modify the intended SQL command when it is sent to a downstream component.
Without sufficient removal or quoting of SQL syntax in user-controllable inputs, the generated SQL query can cause those inputs to be interpreted as SQL instead of ordinary user data. This can be used to alter query logic to bypass security checks, or to insert additional statements that modify the back-end database, possibly including execution of system commands. SQL injection has become a common issue with database-driven web sites. The flaw is easily detected, and easily exploited, and as such, any site or software package with even a minimal user base is likely to be subject to an attempted attack of this kind. This flaw depends on the fact that SQL makes no real distinction between the control and data planes.
Bypass
As mentioned above, the site is a Subdomain for SPR.GOV.MY, and I was able to access into the web (Public), which leads to injection vulnerabilities. The following process :
Access Web
1 |
Access : http://result*****.SPR.GOV.MY |
Access Web
Inject Some SQL Payload
1 |
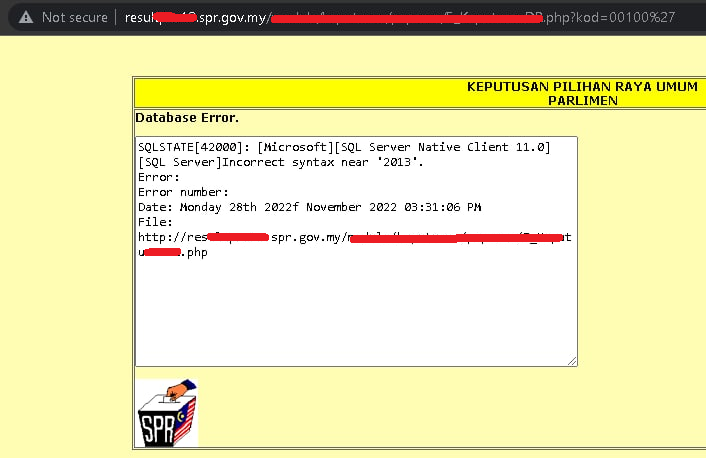
http://result*****.SPR.GOV.MY/mod***/ke*******/paparan/5_***********.php?kod=00100%27< |
SQLi Payload Injection
SQLi Success
http://result*****.SPR.GOV.MY
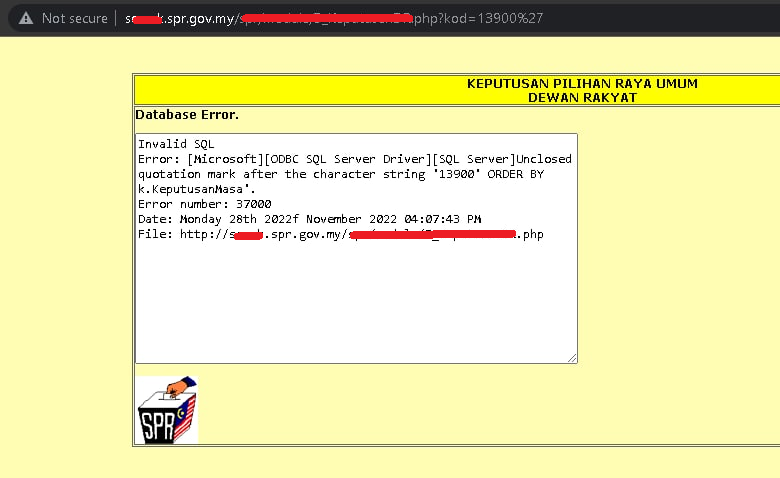
http://s****.SPR.GOV.MY
SQLi Success
CWE-89 SQLi Vulnerabilities
1 |
I was able to inject the system on the server |
CWE-89
Bug Reported
The bug had already been fixed. after my report CWE-89
Sorry about my english, is so bad😅
If you have any questions or suggestions, make sure to hit me in any of these mediums or the comments.
Thanks for reading.